Toilets.Have you ever woken up in the middle of the night, frustrated that you’ve been fumbling around for that darn toilet handle? Have you ever been appalled that you had to actually use your own hands to push down the toilet handle, instead of just saying, “Okay Google, flush the toilet.”
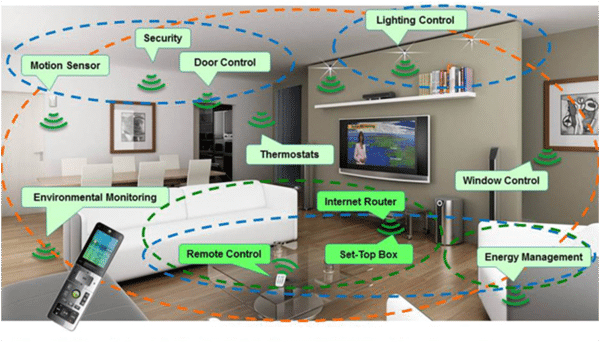
Neither have we, but apparently someone has felt this way because there is a new wave of Smart Toilets hitting the market. Some people prefer to flush by tapping their smartphone (wash your hands first, please), instead of using the handle. If your toilet is now a connected device, you better believe that your entire home will quickly become a fully automated network of devices to make your life easier. Your refrigerator, door locks, thermostat, lights, speakers, smoke alarm, security camera, and all the plugs in your house are just a few examples of some of the smart devices taking us one step closer to our WALL-E world. At this year’s CES 2017 (the premiere consumer electronics and technology tradeshow), home automation and smart home devices took center stage and countless vendors debuted their upcoming products.What does this mean for you? It means that the Internet of Things (IoT) will bring us all a lot of connectivity, efficiency, convenience, and awareness of what all of our stuff is doing at all times. And who wouldn’t want a machine that folds all of your clothes for you? But, with this convenience comes risk. The IoT also creates a vast array of new ways for hackers to exploit you, your home, and your family.You are probably thinking, “Well, I am sure that all of the devices out there can’t all be hackable, can they?” Let me remind you of this exploit that showed the thousands of security cameras that were completely exposed. And, let us not forget about the DDos Attack that ravaged major websites like Twitter, Reddit, and Spotify. This attack was made possible by an IoT botnet, a litany of compromised internet-connected devices puppeteered to attack said websites.The truth is that IoT security is appalling. And, if you have connected devices in your home, or your pocket, you are vulnerable.Gone are the days when hacking was limited to a few rogue geeks in their basement. Hacking is now big business and state-sponsored with major powers like Russia, China, North Korea, and even the United States dedicating teams of people to hacking into your stuff. Hacking has quickly become a multibillion dollar industry running around the clock. Once upon a time, only a few unfortunate folks were victims of these kinds of attacks, but today, hackers are coming after everyone.

So how do you keep hackers out of your smart home?
1) Install the latest updates on all devices
Just like you have to update your Windows operating system, your phone software, your apps, and just about everything technological--smart devices are no exception. While some devices automatically initiate software updates, others require your permission. Take a look at the device’s website to find out how to administer updates and sign-up for email notifications for new releases. Most devices will have some security vulnerability, and these are often addressed in the latest software updates.
2) Always, always, always change the default password (and username)
This is often the biggest mistake users make. In their excitement to get things up-and-running, we often do not take the time to take the basic security measures. But, remember what your high school chemistry always told you while donning his goggles, “Safety first.”Most IoT devices have a default password, and it is usually something simple like, “password”. Manufacturers use this for making the first-time setup more convenient, but it is never the intention that this should always remain the password. Change the default settings as soon as possible. The Mirai botnet exploited this very weakness. Hackers can find your devices on the internet, so at least make it harder for them by changing the password to something complex, and even change the username, if possible.
3) Minimize the Connectivity to the Internet
As a general rule, a wired connection is harder to break into than a wireless connection. Some devices have either ethernet or Wi-Fi connection options, and some even have both. If you can disable whichever connection option you are not using, you can minimize the access hackers have to your devices. Not all devices require an internet connection, and if you do not have a need to connect to the manufacturer’s cloud, you can turn off the internet connectivity to reduce your exposure.
4) Separate your Gadgets from your Home Network
This is a big one for business owners, or any professional, that occasionally works from home. On occasion, you bring home your work laptop that has sensitive client data, or data for the company you own, or work for. Maybe it is just a name, email address, or phone number. But, maybe it is internal financial information, tax documents, or intellectual property for a service or product. Often, laptops contain over a decade worth of business related materials, and if hackers get into your system, your data can be stolen and sold on the black market, or it can be held hostage with ransomware that may cost you thousands of dollars to recover.If your gadgets are on one network, and your critical data (laptops, smartphones, network attached storage, etc.) are on another network, then you can isolate what hackers have access to. Most routers come with an option to create a guest network, to provide temporary internet access to visitors. A guest network will grant a user internet access, without providing them access to your important devices. If you isolate your critical devices to your primary network, then when your smart devices are compromised hackers cannot access the stuff you really want protected.
5) Turn on your Firewall
Almost all modern routers come equipped with a firewall to prevent intrusion and block access from the outside world. Login to your router and make sure the firewall is enabled and blocking any unused ports. While your laptop has built-in security features, your IoT devices do not, and it is like leaving your front door wide open. Turning on the firewall doesn’t close and lock your front door, but it does create a wall (of metaphorical fire) between you and intruders.
6) Disable unnecessary features
If there is a feature that you do not have a need for, then turn it off. Especially, if the device has a built-in camera and microphone. If there is not a disable camera feature, you can turn it to face the wall, so you do not have to worry about someone watching your sleeping baby.
7) Invest in Security Options
Because IoT security is so poor, smart home protection devices have become popular and provide new techniques to specifically prevent these types of intrusion.
8) Setup a Virtual Private Network (VPN)
A Virtual Private Network used to just be something that big businesses used to securely connect offices in remote locations together. But now, with the rise of affordable VPN providers, regular users can make intrusion less likely by encrypting (hiding) your data, your life patterns, and by concealing your location from hackers.
9) Do a Scan

Another option to check your vulnerability is to scan your network with The Internet of Things Scanner. This will not secure your devices, or network, but it can provide you information on where you are vulnerable, so you can begin taking the appropriate steps to fix them. This will scan your network to see if any of your devices are on Shodan. Shodan is “the world's first search engine for Internet-connected devices” that are publicly accessible. You do not want to be found on Shodan. Shodan is often used by hackers to find your security cameras, printers, routers, and other devices that connect to the internet.
Wrapping it Up
While manufacturers are beginning to address some of these issues, the lack of security in IoT devices will continue to be a major concern in the following years, and just as we continue to hear about major data breaches, we will continue to hear about IoT vulnerabilities. The above steps will vastly reduce your exposure to cyber criminals, and will at least make a hacker’s job much more difficult.Breadcrumb is a cybersecurity and executive advisory firm. Located in Central California, we partner with organizations throughout the US, protecting their critical assets from cyber breach. Contact us today for a no-obligation consultation.
Industry Insights
Explore trends, insights, and guidance from technology leaders.

