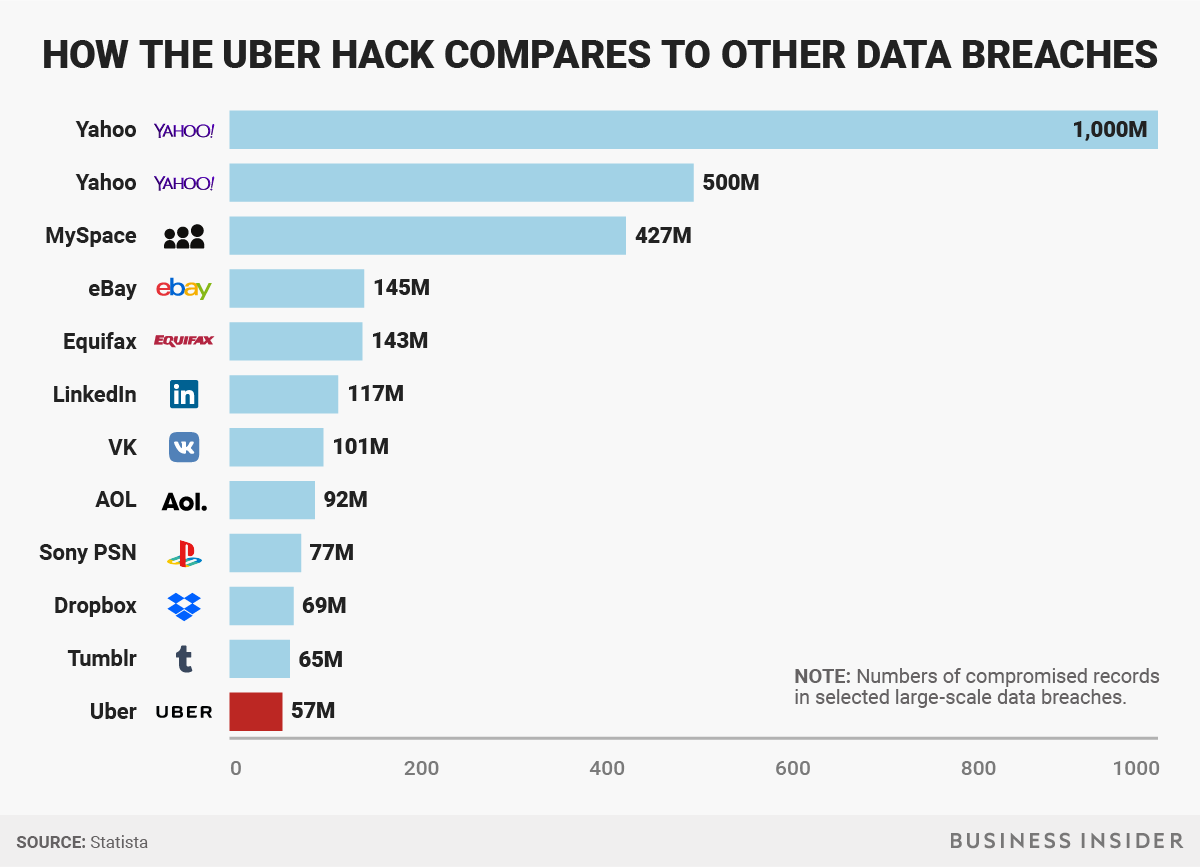
On Tuesday, November 21, Uber officially disclosed a massive data breach that affected 57 million users of the ride-hailing app. The breach originally occurred in October of 2016 with Uber working to conceal it for over a year after paying a $100,000 ransom.
Discovery of the company’s cover-up of the incident resulted in the firing of two employees who led Uber’s response to the hack, said Dara Khosrowshahi, who was named CEO in August following the departure of founder Travis Kalanick.
Khosrowshahi said he had only recently learned of the breach, which happened in October 2016. He said Uber had begun notifying regulators. The New York attorney general has opened an investigation into the data breach, a spokeswoman said.
“None of this should have happened, and I will not make excuses for it,” Khosrowshahi said in a blog post on the company website. “While I can’t erase the past, I can commit on behalf of every Uber employee that we will learn from our mistakes,” Khosrowshahi said. “We are changing the way we do business, putting integrity at the core of every decision we make and working hard to earn the trust of our customers.”
Of the 57 million affected users, 50 million were riders and the other 7 million drivers. The leaked information included names, email addresses, and phone numbers. Additionally, the license numbers of 600,000 drivers were exposed during the breach. Uber says no Social Security numbers or location data was involved.
The company said two hackers stole this data from a third-party server, and then approached Uber demanding $100,000 to delete their copy of the data.
Uber conceded to the demands, and then went a step further. The company tracked down the hackers and forced them to sign nondisclosure agreements, according to the people familiar with the matter. To further conceal the damage, Uber executives also made it appear as if the payout had been part of a “bug bounty” — a common practice among technology companies in which they pay hackers to attack their software to test for security weaknesses.
Uber said it fired its chief security officer, Joe Sullivan, and a deputy, Craig Clark, this week because of their role in the handling of the incident. Sullivan, formerly the top security official at Facebook Inc and a federal prosecutor, served as both security chief and deputy general counsel for Uber.
The company’s decision to conceal the breach and pay the ransom raised concerns among security experts. Many have repeatedly warned against paying hackers to cover up breaches or return stolen data.
“Companies are funding organized crime, an industry of criminals is being created,” said Kevin Beaumont, a cybersecurity expert based in Britain. “The good guys are creating a market for the bad guys. We’re enabling them to monetize what years ago would have been teenagers in bedrooms breaching companies for fun.”
While it is not illegal to pay money to hackers, Uber may have violated several laws in its interaction with them.
Uber is no stranger to data breaches, having experienced a previous attack in May 2014. Uber discovered the event later that year and publicly disclosed the attack in February 2015. In that attack, the names and driver’s licenses of more than 50,000 of the company’s drivers were compromised.
Uber says it does not believe riders need to take any further action but should monitor their credit and other accounts.
Update: Uber already being sued over the massive breach.
Just mere hours after publicly disclosing the breach, and subsequent cover-up, the first lawsuit has been filed.
Filed in a Los Angeles federal court, the suit states that “Uber failed to implement and maintain reasonable security procedures and practices appropriate to the nature and scope of the information compromised in the data breach,” according to Bloomberg.
The lawsuit, launched by a customer, is aiming for class-action status. Meanwhile, New York attorney general Eric Schneiderman has also launched an investigation into the incident.
Breadcrumb is a cybersecurity and executive advisory firm. Located in Central California, we partner with organizations throughout the US, protecting their critical assets from cyber breach. Contact us today for a no-obligation consultation.